October 23, 2015 • read
Technology Tips: October 2015 Edition
|
Skyward IT Services Network Infrastructure and Security Specialists |
Skyward IT Services

Free Online Photo Storage
Are you looking for a free way to back up photos from your smartphone, tablet, or laptop? Did you know that Google offers its account users unlimited (and automatic, if you choose) storage for all of your photos 16 megapixels (MP) or less? Photos larger than 16 MP can be uploaded using your Google account’s 15 GB of storage. (Additional storage can be purchased.) To learn more about Google Photos, go to the Google Photos Help Center or download the photo uploader.How Often Should I Reboot?
The answer to this question depends on what platform you are running.Windows 8, Windows 10, and newer Macs: Only restart your computer as often as is necessary. These devices are designed to stay on. In sleep mode, they use virtually no power – certainly less than they take to shut down and reboot.
Windows 7, Windows Vista, and Windows XP: Shut your computer down at the end of every day. Unlike newer models, the sleep mode on these devices uses more power than the rebooting process requires. Shutting down will save power and better protect your computer.
All Devices: Your computer may need to be rebooted from time to time if you notice it running slower than usual or if your fans are whirring loudly. System updates, software installs, and security scans may also require a restart.
Keyboard Shortcuts
Keyboards have built-in shortcuts that allow you to perform tasks that would otherwise require a mouse. Using keyboard shortcuts can make completing your work easier and faster since you don’t need to take your hand off the keyboard as often. Here are some of the most commonly used keyboard shortcuts: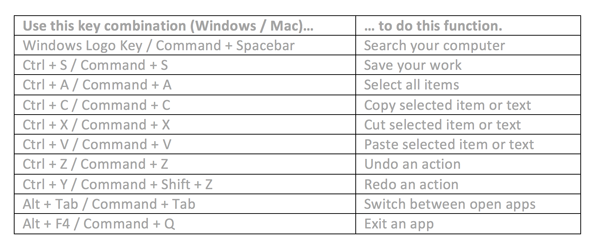
Click here for for a full list of Windows keyboard shortcuts and here for a list of Mac shortcuts.
Malware of the Month
This month’s Malware of the Month is Trojan.Poweliks. This Trojan horse installs a file-less threat and performs click fraud operations on your computer, meaning it clicks on advertisements without your knowledge to earn money for virus creators.Trojan.Poweliks installs itself into the Windows registry where it hijacks many existing entries. It runs when the essential functions of the operating system are performed. It stores its own code within the registry, which allows it to stay on the computer but not have any of its files saved directly to the computer itself.
In some cases, Crypto-type ransomware has been found on computers infected with Trojan.Poweliks. This infection is often due to malvertisement – advertisements infected with malware. Crypto ransomware will encrypt files and then try to get users to pay to decrypt them.
Always be sure your antivirus software is up to date. Up-to-date software is your best defense and will give you the greatest chance of detecting and removing this threat. If your device becomes infected, check with your antivirus provider to get their recommendations for removal.
"Technology will not replace teachers, but teachers who use technology will replace those who do not."
– Anonymous
Need help securing and optimizing your network? Check out the many IT Services we have available and contact us today.
Thinking about edtech for your district? We'd love to help. Visit skyward.com/get-started to learn more.
|
Skyward IT Services Network Infrastructure and Security Specialists |

 Get started
Get started