One thing we know for sure: schools are targets for ransomware.
In fact, between 2021 and 2023, the rate of attacks nearly doubled for K12 schools—from 44% to an astonishing 80%, according to a survey of 3000 education sites by Sophos, a cybersecurity firm based in the United Kingdom. These attacks spawned from many entry points. The top three include:
- Exploited vulnerability (29%)
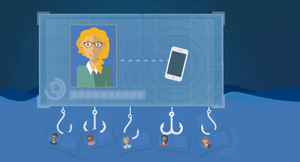
- Compromised credentials (36%)
- Malicious email (19%)
Interoperable systems have fewer manual requirements for data transfers
Fewer manual transfers, connections, and uploads mean fewer weak points for exploitation. Application programming interfaces (APIs) provide a secure, encrypted connection between systems. If you’re able to communicate from system to system directly, it saves time managing authentication processes for multiple systems and reduces the possibility of errors during dual entry processes. After all, each point of authentication is a potential access point for a bad actor who has captured credentials. They may be well guarded, but the door is still there.Choosing a data standard
Take for example Ed-Fi standards. This data standard builds documentation and security into the systems and processes they work with.The benefits don’t end there. Educators, vendors, and tech experts across 36 states have joined the Ed-Fi alliance, agreeing to the standards of data maintenance and protection. It makes it easy to travel between buildings or even to other districts without sacrificing security. Imagine the possibilities as students move or transfer schools!
Choosing edtech solutions made to work seamlessly
What exactly does interoperability look like? Since it’s more of a behind-the-scenes idea, it’s hard to picture. It’s more about what interoperability DOESN’T look like. The fewer times staff has to interact to facilitate transfer from one system to another, the better.This might look like a learning management system (LMS) that communicates seamlessly through an API with your student information system (SIS). With so many different combinations of edtech and so many unique school goals, the combinations really SHOULD be endless—and your vendor should know how to guide you through the process of building up and locking down an airtight system process.
Other benefits help retain great staff
Data standards and interoperable systems not only protect precious data and networks but also make life easier for users. When software does the work of shuffling data around, reporting trends, and mining data to help dig into trends, educators have more time to connect with students and their colleagues. Everyone wins.Encryption works as part of a larger security strategy
The good news is 99% of K12 victims of a cyberattack were able to restore their data from hackers, even if thieves had encrypted the stolen data. This is slightly higher than the global cross-sector average of 97%. The bad news is costs skyrocket when extortion is involved, and schools were way more likely to pay to have data either returned or remain unsold by bad actors. Bad actors are able to encrypt the data they steal, so even if it's recovered, IT pros may not be able to decrypt it. There's no overstating the importance of backing up your data in multiple secure locations.When attacked, most (73%) of K12 schools used backups to restore data. 47% paid ransom to get the data back. It’s worth noting a quarter of respondents used multiple methods to restore data.
While we’ll never stem the criminal attacks, investing in cybersecurity preparedness at least gives K12 tech pros a fighting chance.
Learn more about edtech partnerships:
5 Ways Edtech Companies Show Customers They CareWhen's the Last Time Vendors Asked for Your Feedback?
The Hidden Costs of Poor Edtech Support
The 3 Leading Causes of EdTech Breakups
4 Ways to Save Money in EdTech Purchasing
5 Ways Good EdTech Puts People First
WHAT'S NEXT FOR YOUR EDTECH? The right combo of tools & support retains staff and serves students better. We'd love to help. Visit skyward.com/get-started to learn more.

|
Erin Werra Blogger, Researcher, and Edvocate |
Erin Werra is a content writer and strategist at Skyward’s Advancing K12 blog. Her writing about K12 edtech, data, security, social-emotional learning, and leadership has appeared in THE Journal, District Administration, eSchool News, and more. She enjoys puzzling over details to make K12 edtech info accessible for all. Outside of edtech, she’s waxing poetic about motherhood, personality traits, and self-growth.