This past year, K12 schools became the top targets of ransomware attacks.
In August and September 2020, districts accounted for 57% of reported ransomware attacks. You know the threat is out there, but is your district prepared?
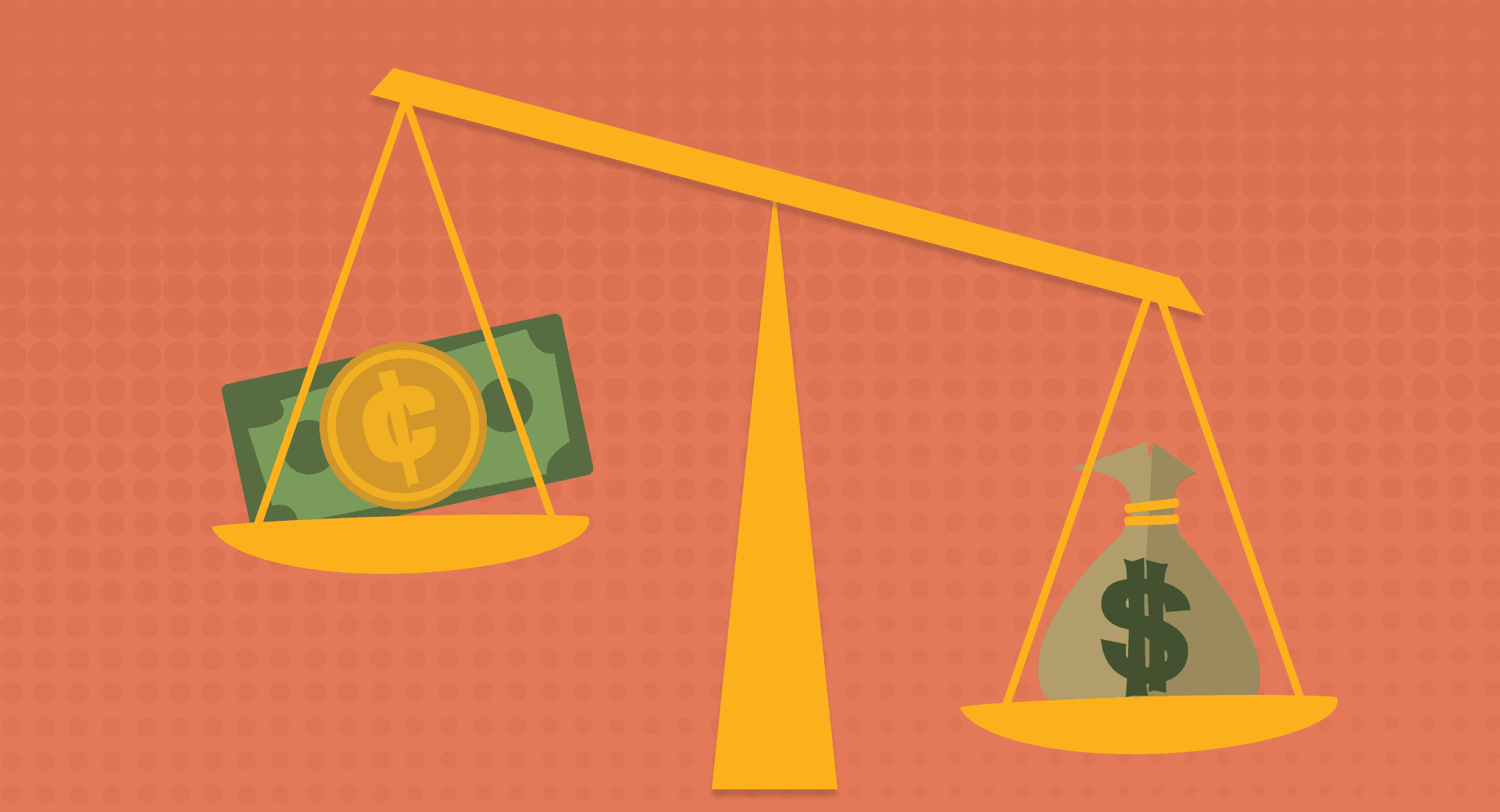
Costs of proactive security
Nothing worth having is free. Create a strong plan when things are going well and you’ll be grateful if disaster strikes.Security teams
Brilliant teams are run by people, not by machines. Salary, training, and planning fall under this category.Has your security team grown in proportion with ransomware risks? According to CoSN’s 2020 EdTech Leadership survey, 69% of districts say they are proactive or very proactive—but less than 20% of respondents had a dedicated full-time employee responsible for cybersecurity. 46% listed it as a shared responsibility, 30% “part of the job,” and 10% ad-hoc. This means an overwhelming majority of school districts run the risk of cybersecurity missteps or passing the buck.
One study by ISC2, a professional IT organization, shows over 4 million cybersecurity jobs are unfilled worldwide. Not only is this a potential blind spot, but it’s an opportunity for students pursuing STEM and computer science fields.
Backup services
Know your data recovery options. Data hosting services may offer multiple options for backup and recovery, but multiple data centers should be a priority. Whether hosting offsite or in person, frequent backups are crucial.Single sign-on
Humans creating passwords is one of the weakest points of any network. Single sign-on uses multiple strategies to strengthen security, as well as makes logging on to the many, many different edtech solutions any given district relies on much easier.Training programs
Constant vigilance is easier when training prompts frequent reminders. Your team members all possess wildly different levels of tech savviness—even the most grizzled veterans of the computer sciences benefit from security training updates. Security training creates a unified set of standards for everyone to follow and may even give you a baseline set of data, so you know where to add training.Crisis communication templates
Hope for the best, prepare for the worst, and create templates when the worst is yet to come. Readers will appreciate calm, collected communication more than a slapdash letter in the event of a data breach.A plan for recovery
What will you do in the event of a breach? If you’re deciding under pressure, you run the risk of missteps. Businesses that have reported taking some time to analyze the data breach saved nearly $100 per record.Cost of reactive security
Now let’s imagine none of the previous planning has taken place. What’s at risk? Besides the possibility of losing access to systems, revealing personal identifiable information, and community backlash, let’s explore the costs of reacting instead of planning.Ransom
While the FBI does not recommend paying ransom, some organizations have done it. Ransom prices have increased as time goes on, and different hackers demand various prices—ranging from $10,000 to hundreds of thousands of dollars.Reactive recovery time
Teams put off or avoid planning for a data breach because they’re busy. Think of it this way: in the event of a breach, there’s no choice but to react, and react quickly. Those reactions are not going to be as careful, thorough, or effective, but they will be much more expensive. Systems paralyzed by a data breach may cause downtime that stretches on for days, leading to huge enforced downtime costs—up to 20 times higher than average ransom requests.Identity monitoring
Organizations may choose to offer their employees credit or identity theft monitoring services post-breach. Typical costs range from $10–30 per person affected. Multiplied by the number of individual records and a school district’s long-term records retention, the number can skyrocket.Reputation
You work hard to earn and keep your community’s trust. Hackers may have tricks to circumvent safeguards, but with thorough and proactive planning they won’t undo this precious work. Your district’s reputation extends to include families’ trust. Your reputation helps retain phenomenal employees, attracts the next round of amazing talent, and builds a strong school culture.Legal settlements and fines
Violations of privacy laws like FERPA carry their own legal costs that suck precious dollars out of your budget fast. It’s not worth it, when you can instead devote some time and energy to a proactive cybersecurity plan.Your district’s data is worth the effort.
Follow-up resource: This culture shift can protect your district
Ditch passwords and embrace passphrases. Here's why it works.WHAT'S NEXT FOR YOUR EDTECH? The right combo of tools & support retains staff and serves students better. We'd love to help. Visit skyward.com/get-started to learn more.

|
Erin Werra Blogger, Researcher, and Edvocate |
Erin Werra is a content writer and strategist at Skyward’s Advancing K12 blog. Her writing about K12 edtech, data, security, social-emotional learning, and leadership has appeared in THE Journal, District Administration, eSchool News, and more. She enjoys puzzling over details to make K12 edtech info accessible for all. Outside of edtech, she’s waxing poetic about motherhood, personality traits, and self-growth.